Tag: Cybersecurity
-
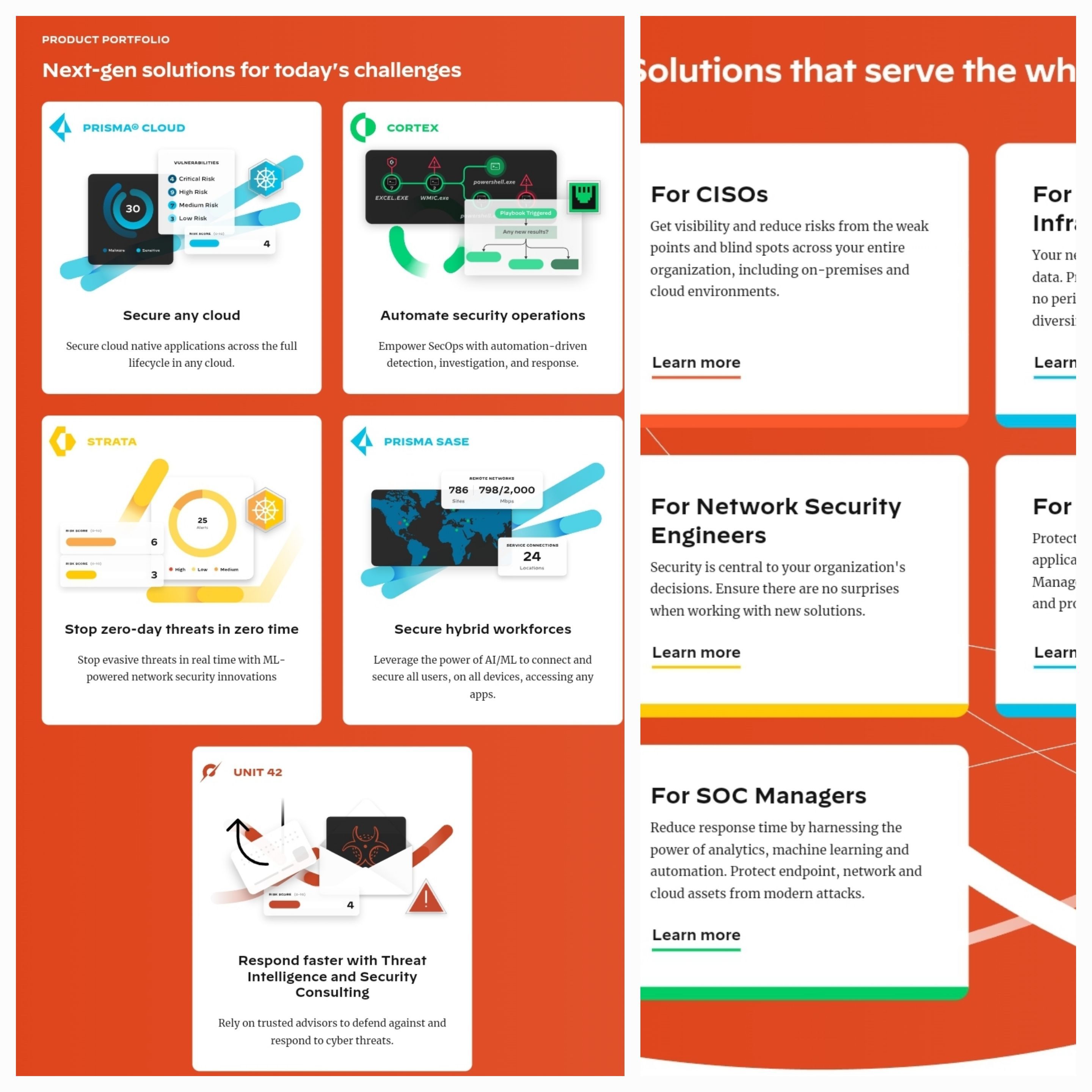
Palo Alto Networks Redefines Cloud Security with Cortex XSIAM for Cloud: Empowering SecOps in the Cloud Era
Discover how Palo Alto Networks’ Cortex XSIAM for Cloud revolutionizes cloud security operations, empowering SecOps teams with advanced capabilities for real-time threat detection and response in the cloud era.
-

FIDO Technology: The Future of Secure Online Authentication
In a world where digital security is paramount, traditional authentication methods are falling short. Dive into the world of FIDO technology, a game-changer that promises to redefine online security. From biometrics to hardware tokens, discover how FIDO is making online authentication more secure and user-friendly. Explore its core principles, the role of biometrics and hardware…
-

Unveiling the Shadows: Safeguarding Financial Transparency in a Shifting World
In an interconnected global economy, the importance of financial transparency cannot be overstated. However, as the world evolves, new risks to transparency emerge. This article explores the evolving landscape of these risks and highlights measures necessary to safeguard the integrity of financial systems. From technological advancements to offshore financial centers, we delve into the challenges…
-
Network and Interconnect Initiative Project: A Comprehensive Guide for Large Organizations
A network and interconnect initiative project is critical for large organizations to build a robust and reliable network infrastructure that can support their operations, growth, and innovation. This comprehensive guide explores the components, importance, and challenges of implementing such a project, including network design, hardware and software selection, interconnectivity, and network management and monitoring. By…
-

Real-Time Network and Device Control: The Ultimate Guide to Responding to Threats
Learn how real-time control of your network and devices can help you respond to cyber threats quickly and efficiently. This comprehensive guide covers real-time control techniques, best practices, and the importance of ongoing network and device security measures. Protect your business and personal information with the ultimate guide to responding to threats.
-
Extending Detection to Every Managed and Unmanaged Connected Device in Your Enterprise: A Comprehensive Guide
As the number of connected devices in enterprises continues to increase, it has become increasingly important for organizations to extend their detection capabilities to every managed and unmanaged connected device. This comprehensive guide explores various technologies, such as EDR, CASB, MDM, and IoT security, to help organizations gain comprehensive visibility into their networks and detect…
-

Attack Surface Management (ASM): A Practical Approach to Understanding and Mitigating Cybersecurity Risks
Attack Surface Management (ASM) is critical for identifying and mitigating potential vulnerabilities in an organization’s infrastructure. This article provides a practical approach to understanding ASM, including identifying assets, determining attack vectors, prioritizing vulnerabilities, mitigating vulnerabilities, and continuously monitoring the attack surface. We also discuss common challenges and best practices for managing an organization’s attack surface.
-

The Role of the CISO in Preventing and Responding to Data Breaches: Case Studies and Best Practices
In today’s digital landscape, data breaches are a significant threat to organizations, and the role of the Chief Information Security Officer (CISO) is critical in preventing, detecting, and responding to these incidents. This article explores the accountability of the CISO in the event of a severe data breach, and highlights some real-life case studies from…
-

Kovai.co Achieves Global SOC2 Type 2 Compliance Certification
Kovai.co, a premier enterprise software and B2B SaaS company, has obtained the Global SOC2 Type 2 compliance certification, demonstrating its commitment to secure client data and software security. The certification guarantees the efficacy of appropriate controls annually and works around five principles, including security, availability, processing integrity, confidentiality, and privacy. This achievement reflects Kovai.co’s dedication…
-

Integrating AI Across Digital Attack Surface For Ransomware Detection
It’s also important for organizations to be aware of the major risks and unidentified leakages that can result from unpatched vulnerabilities, insider threats, and other sources. By taking a proactive approach to security, organizations can minimize their risk of a successful cyberattack and protect their critical assets and sensitive information.
-

Audit Control Points to Reduce Risk of a Cyber Attack
Regularly reviewing these audit control points can help organizations maintain compliance and reduce the risk of a successful cyberattack.
-
Cybersecurity Mesh Architecture Design
A cybersecurity mesh architecture combines multiple security controls, including firewalls, intrusion detection systems, threat intelligence feeds, endpoint security, security information and event management, and disaster recovery and business continuity planning, to provide comprehensive security coverage and improve an organization’s overall security posture.
-

Cybersecurity Consequences vs Cost? What is Your Choice as an Organization?
These groups and individuals represent just a small fraction of the total number of cyber attack groups, hacktivists, and individual hackers operating in the world today. It is important to note that new groups and individuals are constantly emerging and evolving, making it challenging to keep track of the latest developments in the world of…

