Introduction
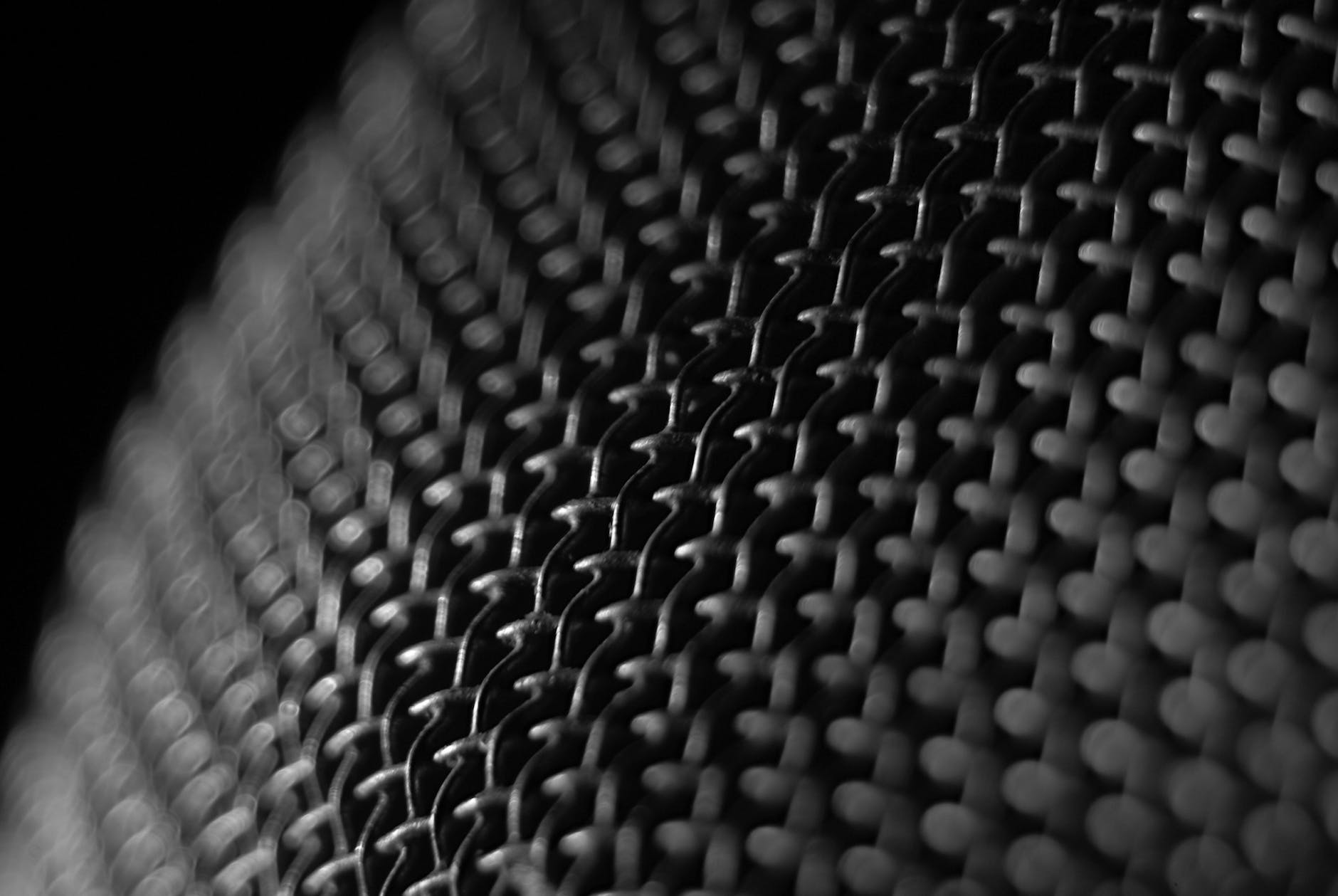
Cybersecurity is becoming increasingly important as technology continues to play a bigger role in our lives. With the increasing number of cyberattacks, it is critical for organizations to have a robust cybersecurity mesh architecture in place to detect, respond, and recover from security incidents in real-time.
What is a cybersecurity mesh architecture?
A cybersecurity mesh architecture is a network of interconnected security controls and systems that work together to provide comprehensive security coverage. It is a layered approach that combines multiple security controls, including firewalls, intrusion detection systems, and threat intelligence feeds, to create a robust defense against cyberattacks.

Why is a cybersecurity mesh architecture necessary?
A cybersecurity mesh architecture is necessary because cyberattacks are becoming more sophisticated and frequent. A single security control may not be enough to protect against the latest threats, so a multi-layered approach is needed to provide comprehensive security coverage. By combining multiple security controls, organizations can improve their overall security posture and reduce the risk of a successful cyberattack.
Components of a cybersecurity mesh architecture
Firewalls: Firewalls are the first line of defense against cyberattacks. They act as a barrier between the organization’s network and the Internet, blocking unauthorized access and traffic.
Intrusion Detection Systems (IDS): IDSs monitor network traffic for signs of a potential attack and alert the security team if they detect something suspicious.
Threat Intelligence Feeds: Threat intelligence feeds provide real-time information about new and emerging threats, allowing organizations to stay ahead of the latest threats and proactively protect their networks.
Endpoint Security: Endpoint security is a critical component of a cybersecurity mesh architecture. It includes tools like antivirus software, firewalls, and intrusion prevention systems (IPS) that are installed on endpoints, such as laptops and mobile devices, to protect against threats.
Security Information and Event Management (SIEM): SIEM is a centralized security platform that aggregates and analyzes log data from multiple sources, including firewalls, IDSs, and endpoints. SIEM can help organizations detect security incidents in real-time and respond quickly.
Disaster Recovery and Business Continuity Planning (DRBCP): DRBCP is a critical component of a cybersecurity mesh architecture. It involves planning and preparation for how an organization will respond and recover from a security incident, ensuring that critical business operations can continue even if a security incident occurs.
Benefits of a cybersecurity mesh architecture
Improved security posture: By combining multiple security controls into a single, integrated architecture, organizations can improve their overall security posture and reduce the risk of a successful cyberattack.
Real-time detection and response: A cybersecurity mesh architecture enables organizations to detect and respond to security incidents in real-time, reducing the impact of a security incident.
Comprehensive security coverage: A cybersecurity mesh architecture provides comprehensive security coverage, covering all aspects of an organization’s security, from the network perimeter to endpoints.
Increased efficiency: A cybersecurity mesh architecture can help organizations automate security processes and reduce manual effort, improving efficiency and reducing costs.
Conclusion
In today’s digital world, cybersecurity is becoming increasingly important. Organizations must have a robust cybersecurity mesh architecture in place to detect, respond, and recover from security incidents in real-time. A cybersecurity mesh architecture combines multiple security controls, including firewalls, intrusion detection systems, threat intelligence feeds, endpoint security, security information and event management, and disaster recovery and business continuity planning, to provide comprehensive security coverage and improve an organization’s overall security posture.

Leave a Reply